Articles
I Love Xbase++ (ILX)
The portal for Xbase++ developers worldwide
The Asset Manager integrated into the Xbase++ Workbench provides an easy interface for viewing, (de-) installing and updating the assets being used in your projects. Behind the scene, the Asset Manager in conjunction with the Workbench, performs the following tasks for you:
Manage asset...
Positioning
If a Smtp or Pop3 endpoint for e-mail exchange requests authorization via the OAuth 2.0 protocol, then this flow-based protocol must be used when communicating with the server to authenticating the client. This may also require displaying a user interface for obtaining the user's...
Background
One of the largest differences in how data is managed between SQL and ISAM is how deleted records are handled. In short:
ISAM: does mark a record as deleted. This way it is out of scope. To really get rid of the record you need to do a time consuming PACK operation.
SQL: does really...
Using native SQL for manipulating data as well as structure (schema) of ISAM-emulated tables is a supported scenario, for example, for being able to share data with non-Xbase++ applications. In the following, the potential pitfalls and general requirements are discussed which must be put into...
Background
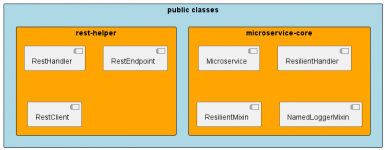
Generally making a service more reliable does not mean to ensure the service works 24/7. This is an old school no more working approach from times where software solutions have been simple, working in defined environments and under full control. But today, even simple software become...
Background
The PGDBE automatically tracks record locks in ISAM-emulated tables, which are set by clients connected to the PostgreSQL server. This is done with the help of the __lock_owner field in the table's meta data. However, when a client dies unexpectantly, has it's network go down or does...
Background
Since the ISAM emulating tables of the PostgreSQL DatabaseEngine are in fact regular SQL tables, it is possible to manipulate them using SQL statements. However, some SQL operations are problematic, as they may lead to inconsistent/incorrect ISAM behavior. In the following, we will...
Background
As you may have already realized, a PostgreSQL server or any SQL server in general is a "relatively" complicated story. The reason for that is basically that the server with the planner tries to replace you as a human. In ISAM you have the data model in mind, also the requirements of...
Overview
By default, the target (.dll or .exe) is created in the directory as implied in the target node of the project file (.xpj). The target [example.exe] is created in the directory where the project file is located. The target [bin\example.dll], on the other hand, is created in the...
Comments for Xbase++ 1.9 users
1. Support for projects with targets in multiple directories
Beginning with Xbase++ version 2.0, complex project scenarios involving targets located in different directories are fully supported. This required changes in the way the targets and the source files...
Background
The Xbase++ PostgreSQL DatabaseEngine provides two different access method to data. First, the ISAM emulating approach which works with dedicated SQL tables only. These SQL tables need to be created using ISAM commands like DbCreate/INDEX ON/OrdCreate or have been upsized from...
Reg-free COM allows using a copy-deployment for applications depending on COM/ActiveX component. As the name implies, Reg-free COM means there's no need to register COM/ActiveX components prior to using them. To achieve this, the application requires one or more manifest files which describe the...
Xbase++ provides INIT procedures, a concepts which allows by a simple declaration of INIT before the procedure keyword to ensure that this procedure is executed before your procedure main is executed. An example is shown below.
INIT PROCEDURE startupMyModule()
// your code is
RETURN...
Background
Sometimes, an application may exhibit symptoms which are hard to understand without having information about the internal state, the workflow and timing of operations. This was not an issue with desktop applications as these basically follow the action->reaction principle. Anybody who...
Background
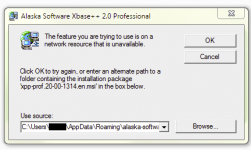
The Update Manager in the Xbase++ Workbench usually provides a seamless update experience; after clicking "Download and Install", the update process usually runs through without further user interaction. However like all processes, it can fail. This article provides some background...
For an overview how COM/ActiveX components can be used from Xbase++ refer to the Xbase++ help ActiveX Overview, expecially to the section Reacting to COM/ActiveX events. Here you can find a working sample how to react to the MS Word quit-event.
Introduction
Email providers such as Google GMail allow authentication of the Smtp and Pop3 client via the OAuth2 security protocol. Furthermore, it is foreseeable that sooner or later other authentications will no longer be allowed. Google has already announced this step.
The OAuth2 security...
Sometimes your application may experience run-time errors such as "error while reading a file" during DbSkip() or DbSeek() operations. These errors often occur in the following scenarios:
large number of concurrent users (>= 15)
large index expressions
large index files (> 500Mb)
In these...
Introduction
This article assumes knowledge of how to use the Asset Manager of the Xbase++ Workbench. You will find an introduction to the Asset Manager of the Xbase++ Workbench in the article Xbase++ Workbench Asset Management.
The Xbase++ OAuth2 asset implements the protocols for the OAuth2...
Introduction
Xbase++ comes with so-called assets. You can consider an asset as a reference implementation. The idea of assets is to formalize the packaging of libraries, frameworks, etc. beyond the Xbase++ core product featureset. In practice, assets are there to clean up the project chaos and...