Articles by Andreas Herdt
I Love Xbase++ (ILX)
The portal for Xbase++ developers worldwide
Introduction
Xbase++ is a versatile programming language that allows developers to create multi-threaded applications easily. In this article, we will explore how to use the Thread class in Xbase++ to create and manage an operating system thread capable of executing different tasks. We will...
Background
The SQL command ALTER TABLE can be used to modify the structure of an ISAM emulated SQL table on the PostgreSQL server. However, in order to preserve the ISAM emulation characteristic, some details have to be taken into account which are described in this article. This article does...
Overview
In this article it is shown how the class AesCrypt() can be specialized to implement some padding schemes for encrypting and decrypting messages.
Background
The Advanced Encryption Standard (AES) standard is a block cipher algorithm that only allows for the encryption of messages in the...
Positioning
If a Smtp or Pop3 endpoint for e-mail exchange requests authorization via the OAuth 2.0 protocol, then this flow-based protocol must be used when communicating with the server to authenticating the client. This may also require displaying a user interface for obtaining the user's...
Overview
By default, the target (.dll or .exe) is created in the directory as implied in the target node of the project file (.xpj). The target [example.exe] is created in the directory where the project file is located. The target [bin\example.dll], on the other hand, is created in the...
For an overview how COM/ActiveX components can be used from Xbase++ refer to the Xbase++ help ActiveX Overview, expecially to the section Reacting to COM/ActiveX events. Here you can find a working sample how to react to the MS Word quit-event.
Introduction
Email providers such as Google GMail allow authentication of the Smtp and Pop3 client via the OAuth2 security protocol. Furthermore, it is foreseeable that sooner or later other authentications will no longer be allowed. Google has already announced this step.
The OAuth2 security...
Introduction
This article assumes knowledge of how to use the Asset Manager of the Xbase++ Workbench. You will find an introduction to the Asset Manager of the Xbase++ Workbench in the article Xbase++ Workbench Asset Management.
The Xbase++ OAuth2 asset implements the protocols for the OAuth2...
Introduction
Xbase++ comes with so-called assets. You can consider an asset as a reference implementation. The idea of assets is to formalize the packaging of libraries, frameworks, etc. beyond the Xbase++ core product featureset. In practice, assets are there to clean up the project chaos and...
It is possible to automate the creation of MS Word documents and also to style the text. For this a Word document is created or opened via the Xbase++ COM/ActiveX layer. The Word instance is represented in Xbase++ by an object of the class AutomationObject(). The document can be manipulated via...
Some technical background
When an application is loaded, the operating system's image loader examines the import directory of the exe file. In this import directory the dll names with their functions (so-called procedure entry points) are listed, which are needed for the application. These...
Problem description
The Xbase++ ISAM emulation uses a native PostgreSQL sequence to calculate the next record number for append operations. Therefore the success of a DbAppend()/APPEND directly depends on the correctness of that PostgreSQL sequence. As a matter of fact the sequence can become...
Background
When a source file ( .prg or .arc) is compiled, then an intermediate file ( .obj or .res ) is created that is finally linked to an executable ( .exe ) or library ( .dll ). The Xbase++ compilers xpp.exe and arc.exe create the intermediates next to their source files. This behavior is...
Background
The PostgreSQL columns of type TEXT and BYTEA allow the storage of large binary data (e.g. PDF documents or images) up to 1GB. If such column types are used in a table their data is accessed like any other data of the record when using the Xbase++ ISAM emulation. With each...
Background
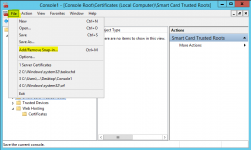
The HttpEndpoint can be bound to an SSL certificate but it must be available in the Windows Certificate Store. This howto article describes how to provide a certificate using the win-acme tool and the IIS web server and how to bind the HttpClient to it.
On the Let's Encrypt homepage...